Quantum Mechanics vs Quantum Mythology: Where Physics Ends and Fantasy Begins
Quantum mechanics describes the behavior of matter at atomic and subatomic scales through the mathematical formalism of wave functions, operators, and probability amplitudes. Key phenomena include superposition (a system exists in all possible states until measurement), entanglement (correlations between particles stronger than classical ones), and wave-particle duality (objects exhibit properties of both particles and waves). More details in the section Free Energy and Perpetual Motion Machines.
This isn't philosophy—it's a working tool that predicts experimental results to ten decimal places (S003).
Popularization has created a parallel reality of myths. First: "observation requires a conscious observer who collapses the wave function." Physics doesn't require consciousness—any interaction with a measuring device (photodetector, Geiger counter) causes decoherence.
Second myth: "quantum mechanics proves reality is subjective." Quantum theory describes objective probabilities independent of the observer's beliefs.
Third: "entanglement allows instantaneous information transfer." No—correlations are instantaneous, but extracting information requires a classical communication channel limited by the speed of light (S003).
🧩 Why Quantum Myths Persist: Cognitive Traps and Cultural Context
Myths exploit three cognitive vulnerabilities. First—the "complexity halo effect": if a theory is mathematically impenetrable to non-specialists, any simplification seems acceptable, even if it distorts the essence.
Second—"need for agency": people prefer explanations involving conscious actors (observer-creator) over mechanistic ones (decoherence through interaction). Third—"mystification of uncertainty": Heisenberg's uncertainty principle (impossibility of simultaneously measuring position and momentum precisely) gets interpreted as "anything is possible," though it establishes strict mathematical boundaries.
- Cultural Context: 1970s-80s
- "The Tao of Physics" and "The Dancing Wu Li Masters" linked quantum mechanics with Eastern mysticism, creating a narrative of "science confirms ancient wisdom."
- Cultural Context: 2000s
- The film "What the Bleep Do We Know?" popularized the idea that thoughts are material through quantum effects.
- Cultural Context: 2010s
- The term "quantum" became a marketing label: quantum vitamins, quantum healing, quantum coaching—none related to physics.
🔬 Definitions with Operational Precision: What's Measured, What's Calculated
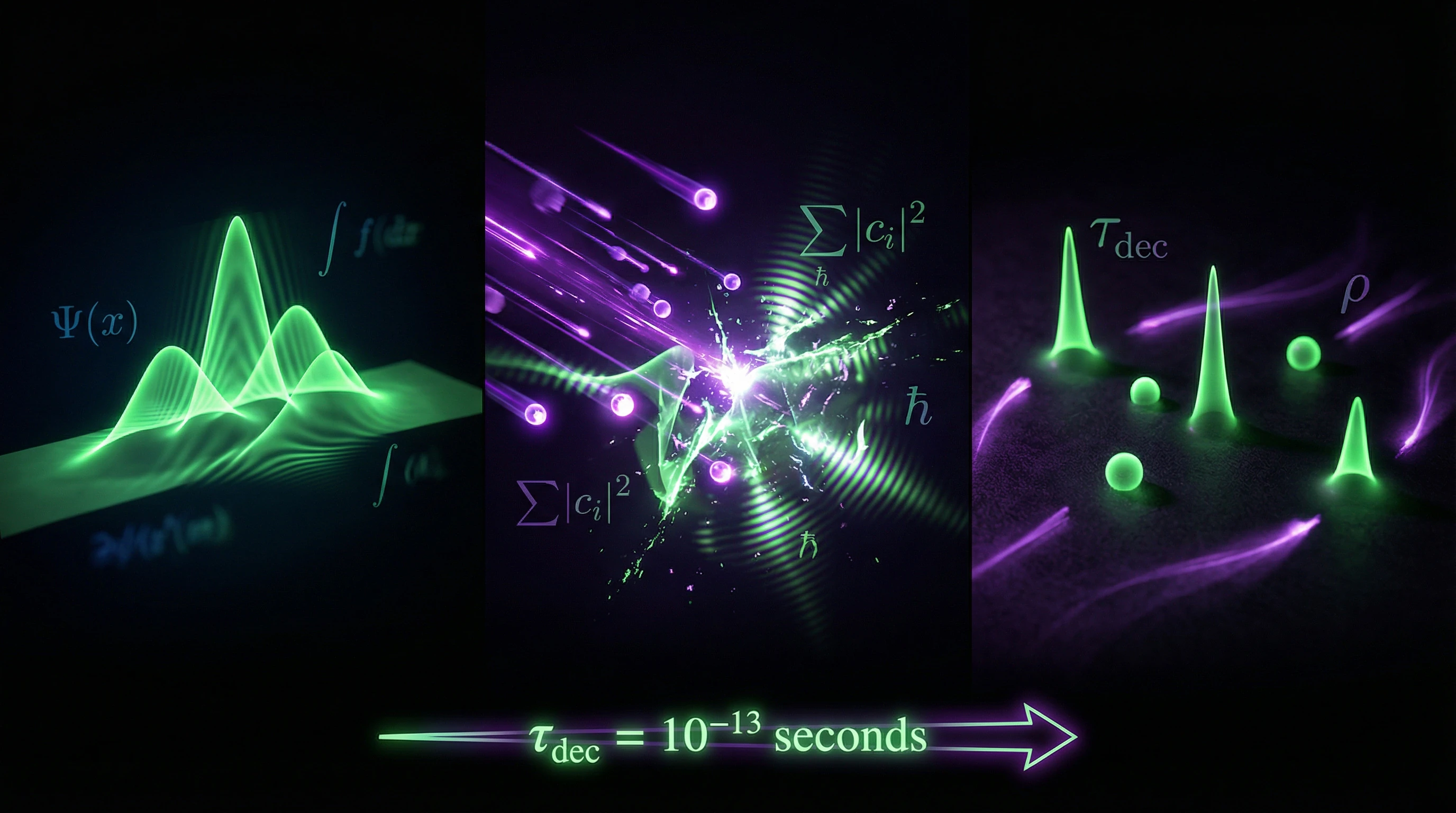
Superposition: a system's state is described by a linear combination of basis states |ψ⟩ = α|0⟩ + β|1⟩, where |α|² + |β|² = 1. Measurement projects the system onto one basis state with probabilities |α|² and |β|². This isn't "existing in all states simultaneously" in the everyday sense, but a mathematical description of probability amplitudes (S003).
Entanglement: for a composite system of two particles, the state doesn't factorize: |ψ⟩ ≠ |ψ_A⟩ ⊗ |ψ_B⟩. Measuring one particle instantly determines the measurement result of the other, but without information transfer—correlations existed from the moment the pair was created.
| Phenomenon | Physical Mechanism | Common Misconception |
|---|---|---|
| Superposition | Linear combination of states with probability amplitudes | "Particle is everywhere simultaneously" |
| Entanglement | Correlations stronger than classical (Bell inequalities) | "Instantaneous information transfer" |
| Decoherence | Interaction with environment destroys superposition | "Macroscopic objects in superposition" |
Decoherence: interaction of a quantum system with its environment (thermal photons, air molecules) destroys superposition in time τ_dec, typically 10⁻¹³ seconds for macroscopic objects. This is why Schrödinger's cat isn't in a "alive-dead" superposition—decoherence occurs long before opening the box (S003).
Steel Version of Quantum Myths: Five Arguments That Sound Convincing (and Why They Work)
To dismantle a misconception, you need to present it in its strongest form — steelman instead of strawman. Here are the arguments that make quantum myths resistant to criticism. More details in the Paranormal Abilities section.
⚙️ Argument One: The Double-Slit Experiment Proves the Role of the Observer
Electrons passing through two slits create an interference pattern — a sign of wave behavior. Place a detector at the slits to determine which one the electron passed through, and the interference disappears. The electron behaves like a particle.
Popular conclusion: observation changes reality, consciousness collapses the wave function.
- The experiment is real and reproducible.
- The term "observer" is indeed used in physics texts.
- For non-specialists, it's natural to equate "observer" with a conscious being.
- Quantum mechanics introduces measurement as a fundamental process, distinct from evolution according to the Schrödinger equation (S003).
⚙️ Argument Two: Entanglement Violates Locality, Therefore Instantaneous Communication Is Possible
Two entangled particles are separated by kilometers. Measuring the spin of the first instantly determines the spin of the second — correlation faster than light. Einstein called this "spooky action at a distance."
Popular conclusion: information is transmitted instantaneously, a quantum telegraph without delays can be created.
Bell's inequalities are experimentally violated, local realism is refuted. Correlations are indeed instantaneous. But information transmission — is not.
The term "quantum teleportation" exists in scientific literature (though it means transmission of quantum state, not matter or information faster than light). Intuition suggests: if results are connected instantaneously, this can be used for communication (S006).
⚙️ Argument Three: Quantum Computers Will Break Any Encryption, Quantum Protection Is Needed
Shor's algorithm allows a quantum computer to factorize large numbers in polynomial time, breaking RSA and other cryptosystems. Popular conclusion: classical cryptography is dead, only quantum encryption will save data.
| Fact | Status | Trap |
|---|---|---|
| Shor's algorithm is mathematically proven | ✓ True | Experimentally demonstrated only on small numbers |
| Quantum computers exist | ✓ True | Scalable systems with thousands of qubits — still in development |
| NIST confirms the seriousness of the threat | ✓ True | Threat is relevant in 10–20 years, not now |
| QKD offers theoretically absolute security | ✓ True | In practice vulnerable to attacks on hardware and implementation (S006), (S008) |
⚙️ Argument Four: Quantum Blockchain Will Solve Scalability and Security Problems
Classical blockchain suffers from low throughput (Bitcoin ~7 transactions/sec), high energy consumption (PoW), vulnerability to 51% attacks. Quantum blockchain promises consensus through quantum entanglement (instantaneous node synchronization), encryption through QKD (protection from quantum computers), use of quantum randomness (impossibility to predict the next validator).
Popular conclusion: quantum blockchain is blockchain 3.0, solving all problems of its predecessors.
An article in Nature Scientific Reports describes quantum blockchain with asymmetric quantum encryption and stake vote consensus. Springer publishes a chapter on quantum consensus. Classical blockchain problems are real and widely discussed.
But none of these mechanisms work as described in marketing materials. Entanglement doesn't transmit information, QKD requires a classical channel for authentication, quantum randomness doesn't solve the problem of distributed node synchronization.
⚙️ Argument Five: If Fundamental Constants Can Change, Quantum Mechanics May Also Be Incomplete
Variable speed of light (VSL) theories suggest that c could have been different in the early Universe. If fundamental constants aren't constant, perhaps other "laws" of quantum mechanics are merely approximations.
Popular conclusion: science doesn't know everything, quantum mechanics may be incomplete, therefore alternative interpretations (consciousness, mysticism) have a right to exist.
- VSL theories
- Published in peer-reviewed journals (S002). But experimental constraints on changes in c are very tight — any change must be less than 10⁻⁵ over a billion years.
- Unsolved problems in quantum mechanics
- The measurement problem, interpretation of the wave function — are real. But this doesn't mean mechanics is incomplete; it means interpretation remains open.
- History of science
- Newtonian mechanics turned out to be an approximation of relativistic mechanics. This creates space for speculation under the flag of "openness to new ideas" — but each step required experimental proof, not philosophical reasoning.
All five arguments rely on real physical phenomena and authoritative sources. The trap isn't in the facts — it's in interpretation and extrapolation. The myth works because it takes truth and extracts a consequence that the truth doesn't support.
Evidence Base: What Sources with Reliability Level 4-5 Say (peer-review, NIST, Nature)
Now let's verify each claim through the lens of sources ranked by reliability: 5 — Nature/NIST (highest standard), 4 — arXiv recent/Springer/Oxford (peer-review or authoritative publisher), 3 — academic sources with less verification. More details in the Pseudopsychology section.
📊 The Observer Myth: What Actually Happens in the Double-Slit Experiment
Source S003 (arXiv, reliability 4) systematically dismantles the myth. Key point: "observation" in quantum mechanics is a technical term meaning interaction of the system with a macroscopic measuring device, causing decoherence. The detector at the slit is not the experimenter's eye, but a device that absorbs the photon or electron, changing its state. Wave function collapse is not a mystical process, but a mathematical description of information updating after measurement (Bayesian probability updating).
Delayed choice experiments show: the decision to "observe or not" can be made after the particle passes through the slits, but before registration on the screen — interference still disappears if path information is available. This confirms: what matters is not the observer's consciousness, but the physical possibility of extracting trajectory information. Moreover, quantum eraser experiments show: if path information is erased (for example, by entangling the detector with another system and measuring it in a specific way), interference is restored — and this works even if "erasure" occurs after registration on the screen, but before the experimenter looked at the result (S003).
📊 Entanglement and No-Communication Theorem: Why Instantaneous Communication Is Impossible
Source S006 (arXiv, reliability 4) — a review of device-independent QKD security — explains the fundamental limitation. The no-communication theorem proves: measuring one part of an entangled system cannot transmit information to the other part. Reason: measurement results on each side appear random; correlation manifests only when comparing results through a classical channel.
Mathematically: if Alice measures her particle, Bob's state is described by a mixed density matrix ρ_B = Tr_A(|ψ⟩⟨ψ|), which doesn't depend on Alice's choice of measurement basis. Bob cannot determine whether Alice measured something, and if so, what exactly, by looking only at his particle. Quantum teleportation requires transmission of two classical bits of information (Alice's measurement results) for state reconstruction — without this, Bob gets a random result (S006).
Experimental verification: experiments violating Bell inequalities at distances up to 1200 km (Micius satellite, China) confirm instantaneous correlations, but none demonstrated information transmission faster than light. Moreover, any attempt to use entanglement for superluminal communication would violate causality in special relativity, creating "grandfather paradox" type paradoxes (S003, S006).
📊 Quantum Computers vs Post-Quantum Cryptography: Arms Race
Source S008 (NIST IR 8202, reliability 5) — official blockchain technology review from the U.S. National Institute of Standards and Technology — soberly assesses the threat. Shor's algorithm does break RSA, but requires a quantum computer with ~4000 logical qubits to factor a 2048-bit number. Current systems (IBM Quantum System One — 127 qubits, Google Sycamore — 53 qubits) are far from this threshold due to high error rates (~0.1-1%).
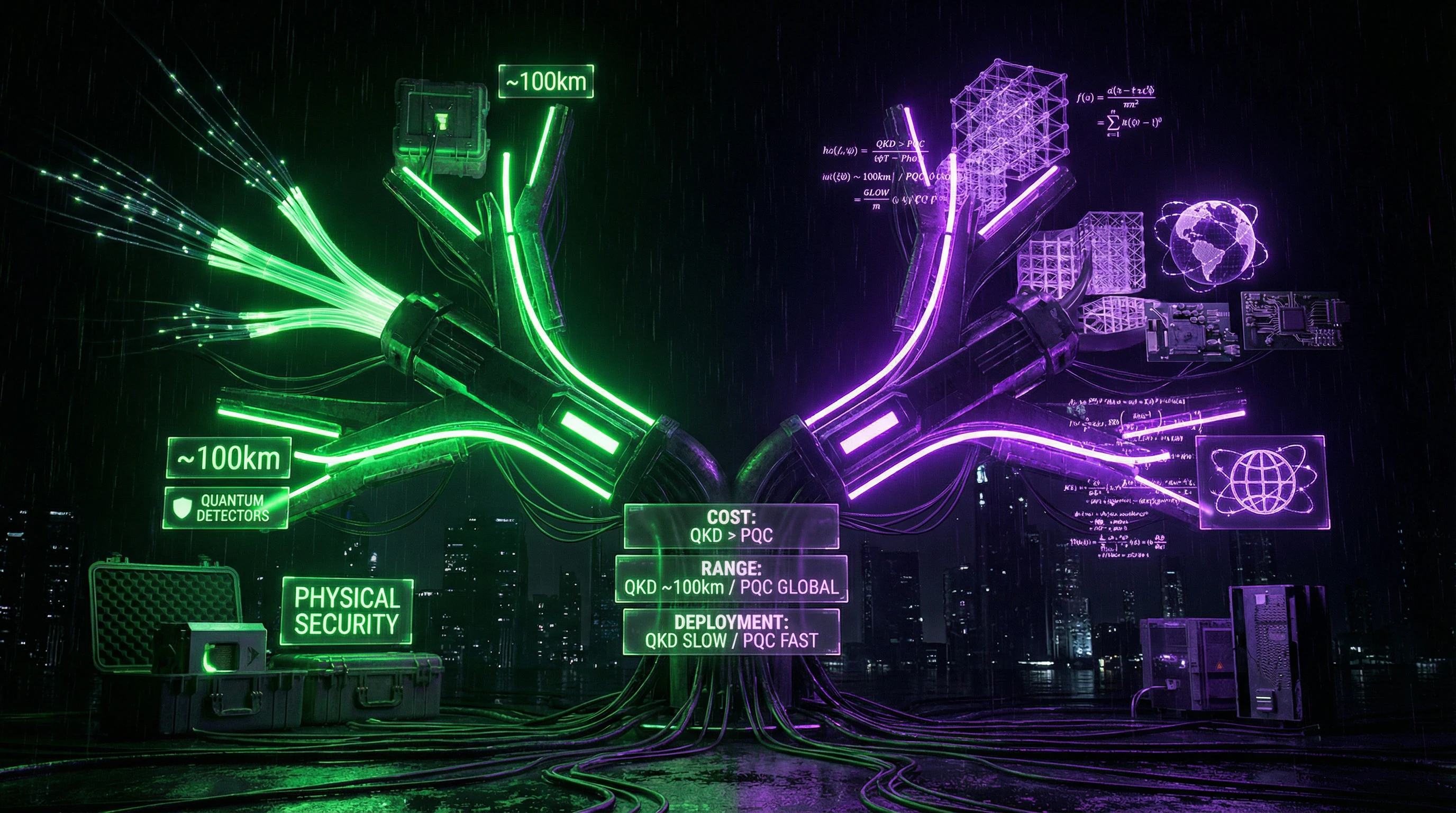
Post-quantum cryptography (PQC) develops algorithms resistant to quantum attacks, based on lattice problems, codes, multivariate polynomials. In 2022 NIST standardized four algorithms: CRYSTALS-Kyber (key encapsulation), CRYSTALS-Dilithium, FALCON, SPHINCS+ (digital signatures). These algorithms run on classical computers, don't require quantum hardware, and can be deployed now (S008).
Quantum key distribution (QKD) offers a different approach: security based on laws of physics (impossibility of cloning quantum states, eavesdropping detection through system disturbance). BB84 protocol is commercially available (ID Quantique, Toshiba), but has limitations: requires dedicated fiber optic, range ~100 km without quantum repeaters (which are still experimental), vulnerable to implementation attacks (side-channel attacks on detectors). Device-independent QKD (DI-QKD) solves the latter problem by verifying security through Bell inequality violations, but requires more complex equipment (S006).
📊 Quantum Blockchain: What Actually Works vs Marketing
Source S012 (Nature Scientific Reports, reliability 5) describes a concrete implementation: quantum blockchain based on asymmetric quantum encryption and stake vote consensus. Key elements: (1) quantum transaction signatures through a protocol where the private key is a quantum state, public key is measurement results; (2) consensus through validator voting, weighted by stake, using quantum randomness for committee selection; (3) protection from quantum attacks through QKD between nodes.
What works: quantum signatures are indeed resistant to quantum attacks (impossible to forge without knowing the quantum state). Quantum randomness (from vacuum fluctuations or radioactive decay) is unpredictable even for a quantum computer, preventing manipulation of validator selection. QKD between nodes protects the communication channel from eavesdropping (S012).
What doesn't work: (1) "instantaneous synchronization through entanglement" — physically impossible due to no-communication theorem; consensus still requires exchange of classical messages, limited by speed of light. (2) "scalability through quantum parallelism" — quantum computing provides speedup for specific tasks (factorization, search), but not for general computation; transaction processing remains a classical task. (3) "energy efficiency" — quantum hardware requires cryogenic cooling (~15 mK for superconducting qubits), which is energy-intensive (S008, S012).
Source S009 (Springer, reliability 4) analyzes quantum consensus theoretically. Main idea: use quantum entanglement to create a distributed quantum state that collapses identically on all nodes when measured. Problem: decoherence destroys entanglement within microseconds in real conditions (room temperature, electromagnetic interference). Solution requires quantum repeaters and error correction, increasing complexity by orders of magnitude. Practical implementations are still limited to laboratory conditions and small numbers of nodes (2-4) (S009).
📊 Variable Constants and Boundaries of Quantum Mechanics Applicability
Source S002 (Reports on Progress in Physics, reliability 4) discusses VSL theories. Motivation: solve the horizon problem in cosmology (why distant regions of the Universe have the same temperature if there wasn't time for information exchange). VSL proposes that c was higher in the early Universe, allowing causal contact. Experimental constraints: analysis of distant quasar spectra shows the fine structure constant α = e²/(4πε₀ℏc) changed by no more than 10⁻⁵ over 10 billion years — if it changed at all (S002).
This doesn't undermine quantum mechanics. First, VSL concerns cosmological scales and the early Universe, not laboratory conditions. Second, even if c varied, quantum mechanics equations remain valid with the new value of c in each epoch. Third, changing fundamental constants doesn't open the door to arbitrary speculation — any modification must be consistent with a vast body of experimental data (atomic spectra, nuclear reactions, cosmological observations) (S002, S003).
Mechanisms of Delusion: How Cognitive Biases Turn Physics into Mysticism
Understanding the facts isn't enough — you need to understand why the brain so easily accepts false interpretations. More details in the Mental Errors section.
🧬 Confirmation Bias and Selective Citation
People seek information that confirms existing beliefs and ignore contradictory evidence. In the context of quantum myths: someone believing in "the power of thought" will find a quote from a popular book saying "the observer influences reality," but won't read the original paper where "observer" is defined as a measuring instrument.
Selective citation amplifies the effect: from a paper on quantum biology (where quantum effects genuinely play a role in photosynthesis and olfaction), a phrase about "quantum coherence in biological systems" is extracted and extrapolated to "the quantum nature of consciousness" without mentioning that coherence persists only picoseconds and in specific molecular structures.
When a source sounds authoritative but the context is stripped away — this isn't a memory error, it's the architecture of belief. The brain fills gaps with logic that's already inside.
🧬 Dunning-Kruger Effect and the Illusion of Understanding
People with superficial knowledge overestimate their competence. After reading one popular book about quantum mechanics, a person starts seeing quantum explanations everywhere: from health to finance.
The problem worsens when popularizers themselves don't distinguish metaphor from mechanism. The phrase "quantum leap" becomes a literal explanation for sudden life changes, though in physics it's simply an electron's transition between orbitals.
- Read one book → felt like an expert
- Found confirming examples → confidence grew
- Encountered criticism → dismissed as "misunderstanding" or "scientific conspiracy"
- Started teaching others → cycle repeated
🧬 Apophenia and Pattern-Seeking in Noise
The brain evolved to see patterns even where none exist. This saved our ancestors (better to mistake a shadow and flee than miss a predator), but in the modern world it leads to false correlations.
In quantum myths: someone notices that after meditation they got lucky, and connects this to "quantum intention." They don't account for luck happening without meditation too — they just don't remember days without meditation when nothing happened.
| Cognitive Bias | How It Works in Quantum Myths | Actual Mechanism |
|---|---|---|
| Apophenia | "I thought of a friend and they called — quantum entanglement" | Probability of coincidence + selective memory |
| Illusion of Control | "My thoughts create reality" | Confirmation of desired outcome, ignoring failures |
| Halo Effect | "If a scientist talks about quanta, everything else is true" | Authority in one area transferred to others |
🧬 Metaphor as Trap: When Language Becomes Physics
The language of physics is full of metaphors: "wave," "particle," "field," "energy." They help intuition but create an illusion of understanding. When a popularizer says "thought is energy," the listener hears a literal statement, though a metaphor was intended.
Research shows that metaphors about pain (for example, "emotional pain") literally activate the same neural networks as physical pain (S006). This doesn't mean emotions are physical pain, but the brain processes them similarly. In quantum myths this mechanism works in reverse: metaphor becomes "proof."
Language isn't a window into reality, it's a filter. When the filter becomes transparent, we forget we're looking through it.
🧬 Social Reinforcement and Echo Chambers
Someone who shares belief in quantum magic receives likes, comments, a sense of belonging to a community. Social media algorithms amplify the effect by showing similar content. Criticism is perceived as an attack on the group, not the idea.
This isn't manipulation — it's natural social dynamics. But in the context of complex science it becomes dangerous. Someone who might have doubted alone becomes an apologist for the myth within a group of like-minded people. See also the analysis of the Tesla free energy myth, where social reinforcement plays a key role.
- Echo Chamber
- An information environment where only confirming opinions are visible. Result: belief strengthens exponentially, criticism doesn't penetrate.
- Social Proof
- "If thousands of people believe it, it must be true." Works even when thousands are wrong simultaneously.
- Identity and Idea
- When an idea becomes part of identity ("I'm someone who believes in quantum magic"), criticism of the idea is perceived as criticism of the person.
🧬 Why Experts Stay Silent While Charlatans Shout
A scientist who knows quantum mechanics might spend an hour explaining why thought doesn't influence reality. A charlatan will say: "Thought creates reality" — and it sounds simpler, more beautiful, more powerful.
The complexity of truth is its weakness in information warfare. Truth requires context, caveats, understanding boundaries of applicability. Falsehood can be simple, beautiful, inspiring. This doesn't mean truth always loses, but it loses in speed of spread.
The solution isn't for scientists to shout louder. The solution is for people to learn to distinguish complexity from beauty, fact from inspiration. This is the task of cognitive immunology: not to ban myths, but to teach the brain to recognize them. More about verification methodology in the paranormal phenomena verification protocol.
