What the Internet of Things Really Is — and Why "Smart Home" Is a Euphemism for "Surveilled Home"
The Internet of Things (IoT) is a global network of physical objects equipped with sensors, processors, and communication modules capable of collecting, exchanging, and processing data without human intervention. IoT infrastructure encompasses medical devices, unmanned aerial vehicle control systems, intelligent campuses, and household devices — from refrigerators to door locks (S003, S004).
The key distinction between IoT and traditional computer systems is continuous data collection and autonomous decision-making. While you can turn off a smartphone, a smart thermostat, medical implant, or surveillance system operates constantly, generating streams of information about your location, physiological parameters, behavioral patterns, and social connections. More details in the Reality Validation section.
The integration of artificial intelligence into IoT systems amplifies this problem: machine learning algorithms analyze data in real time, identifying correlations that users themselves don't recognize (S006).
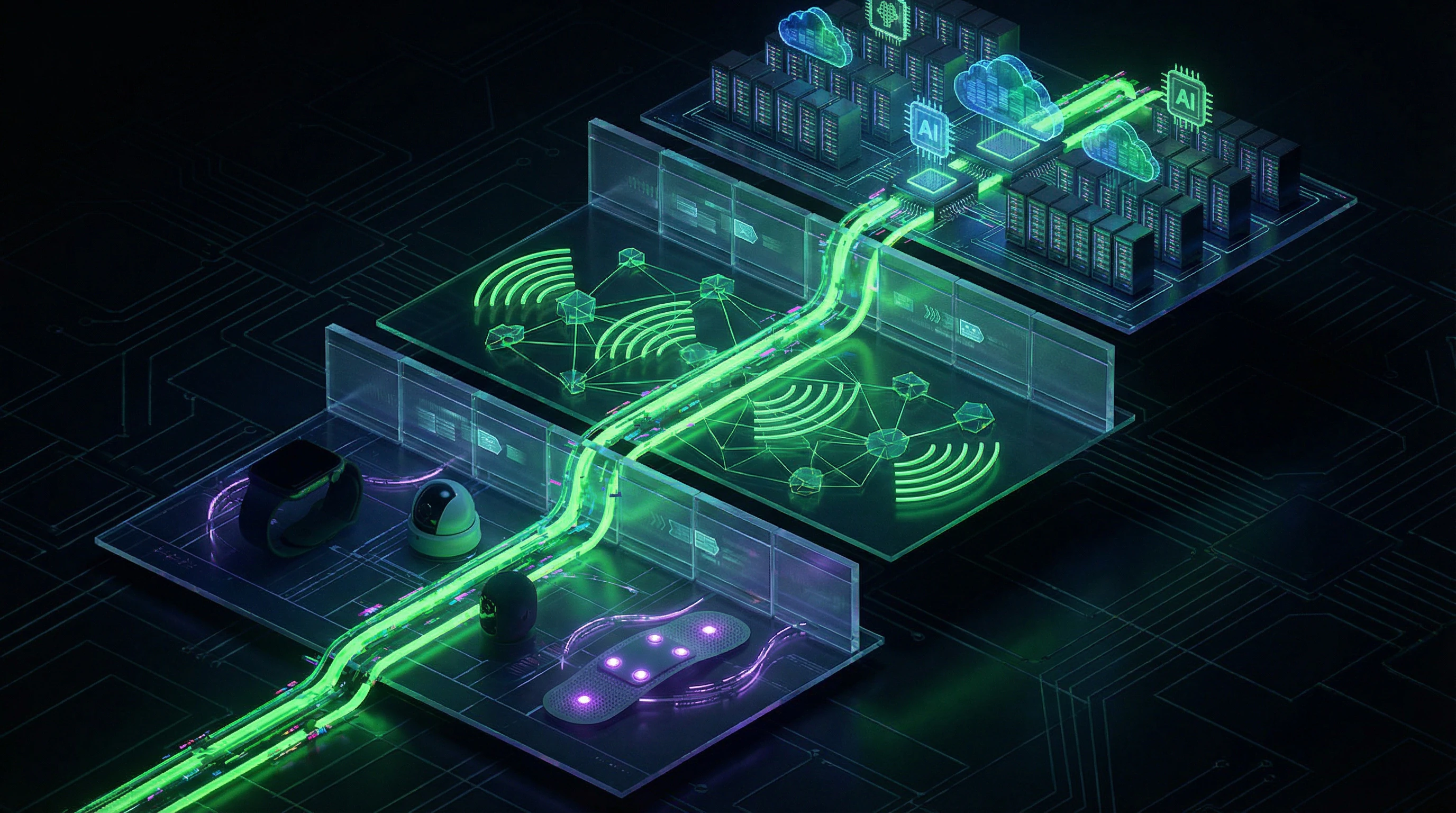
Three Layers of IoT Architecture and Data Collection Points
The technical architecture of IoT consists of three layers, each representing a privacy threat.
| Layer | Components | Vulnerability Points |
|---|---|---|
| Perception (perception layer) | Sensors: accelerometers, microphones, cameras, biometric scanners | Primary collection of data on heart rate, voice, movements, body temperature |
| Network (network layer) | Wi-Fi, Bluetooth, 5G, LoRaWAN, Zigbee | Interception of unsecured connections, unencrypted transmission |
| Application (application layer) | Cloud storage, profile aggregation, decision-making | Third-party access: advertising networks, analytics companies, government agencies |
At each layer, data can be intercepted, transmitted without protection, or misused. Cloud storage is a particularly critical point: access is granted not only to device manufacturers but also to numerous third parties.
Definitional Boundaries: What Falls Within the IoT Ecosystem and What Remains Outside
- Not IoT:
- Traditional computers and smartphones (require active user participation), isolated devices without network connectivity, systems with fully local data processing without cloud transmission.
- Are IoT:
- Wearable medical sensors transmitting data to physicians (S003); UAV control networks with remote management; "smart campus" systems tracking movements; home assistants with constantly active microphones.
This boundary blurs with the development of edge computing — technology where part of data processing occurs on the device itself rather than in the cloud. Manufacturers position this as enhanced privacy, but research shows that even with local processing, metadata (activity times, usage frequency, request types) is still transmitted to servers for "service improvement" (S006).
Local data processing isn't the absence of surveillance, but its reformatting: instead of content, you transmit behavioral patterns, which are often more informative than the data itself.
Steel Man: Seven Arguments Defending IoT Ecosystems — and Why They Sound Convincing
Before examining the risks, we must honestly present the strongest arguments from IoT proponents. This is not a straw man, but a steel man — the most convincing version of the opposing position. Learn more in the Epistemology section.
🔬 Argument 1: Medical Revolution — IoT Saves Lives Through Continuous Monitoring
IoT systems for medical diagnostics detect pathologies at early stages when traditional methods are ineffective. Internet of Things networks for patient diagnosis based on iris data enable remote health analysis, identifying signs of diabetes, hypertension, and neurological disorders without a doctor's visit (S010).
Wearable cardiac monitors detect arrhythmias in real time, preventing heart attacks. For patients with chronic conditions, this isn't convenience — it's a matter of survival.
IoT defenders' counterargument: yes, data is collected, but the alternative is death from undiagnosed disease. Privacy is a privilege of the healthy. The sick choose life, not abstract data protection.
🧬 Argument 2: Resource Optimization — Smart Cities Reduce CO₂ Emissions and Energy Consumption
IoT infrastructure in "smart campuses" optimizes electricity, water, and heating consumption based on real data about human presence and weather conditions. Research on IoT applications in intelligent campuses demonstrates 20–30% reductions in energy consumption through adaptive control of lighting, heating, and ventilation (S004).
At city scale, this means millions of tons of prevented CO₂ emissions.
IoT defenders argue: the climate crisis is an existential threat before which privacy concerns are secondary. Collecting data on movement and energy consumption is the necessary price for planetary survival.
⚙️ Argument 3: Security Through Transparency — IoT Prevents Crime and Terrorism
IoT networks for UAV management are used to monitor critical infrastructure, patrol borders, and search for missing persons (S003). Video surveillance systems with facial recognition help apprehend criminals. Smart locks and motion sensors prevent theft.
- Statistics show correlation between IoT device density and reduced crime rates in neighborhoods
- If you have nothing to hide, you have nothing to fear
- Those demanding privacy aren't protecting freedom, but the ability to break laws with impunity
🧠 Argument 4: Personalization as a Right — IoT Creates Services Perfectly Suited to You
Integration of artificial intelligence into IoT enables hyperpersonalized services: music recommendations adapted to your heart rate during workouts; routes accounting for your fatigue and stress; educational programs adjusting to your learning speed (S006).
This isn't surveillance, but service that's impossible without deep user understanding.
Defenders argue: rejecting IoT means rejecting progress. Do you want to return to an era when everyone received the same low-quality service?
🧷 Argument 5: Economic Efficiency — IoT Reduces Costs for Business and Consumers
Predictive maintenance systems based on IoT sensors prevent equipment failures, reducing production downtime by 40–50%. Smart electricity meters allow consumers to save on rates by shifting load to nighttime hours.
Logistics companies optimize delivery routes, lowering product costs. These benefits are impossible without data collection and analysis.
- Defenders' Argument
- Privacy is a luxury only the wealthy can afford. For most people, saving 20% on electricity bills matters more than abstract data breach risks.
🔬 Argument 6: Scientific Progress — IoT Generates Data for Breakthrough Research
Data arrays collected by IoT devices are used for epidemiological research, studying social processes, and developing new medications. Analysis of fitness tracker data from millions of users revealed early signs of COVID-19 before official symptoms appeared.
Without this data, science is blind. The connection between algorithms and data becomes the foundation for understanding human behavior at population scale.
IoT defenders: refusing data collection means refusing the possibility of saving millions of lives in the future. Your privacy versus people's lives — what will you choose?
🧭 Argument 7: Voluntariness and Control — Users Decide What Data to Share
Modern IoT devices offer privacy settings: you can disable data transmission, delete history, and limit third-party access. Manufacturers claim compliance with GDPR and other regulations.
If you don't like the terms, don't buy the device — it's a free market. The problem isn't the technology, but irresponsible users who don't read user agreements and don't configure privacy settings. Education, not bans — that's the solution.
- Lateral Reading
- Reviewing user agreements requires critical information analysis skills that most users haven't developed.
Evidence Base: What IoT Systems Research Actually Shows — and Where Facts End, Speculation Begins
We'll test each pro-IoT argument for strength through available sources and identify data gaps. More details in the Statistics and Probability Theory section.
📊 Medical IoT: Effectiveness vs. Risks — What the Numbers Say
Research on IoT for medical diagnostics demonstrates the technical feasibility of remote health analysis (S003). But publications contain no data on accuracy, false positive rates, or comparisons with traditional methods.
There's no information about biometric data storage, access controls, or protection mechanisms against breaches.
Critical gap: not a single available study provides long-term statistics on medical IoT system security. We know the technology works, but we don't know how many times patient data has leaked, been sold, or used against their interests — for example, to deny insurance coverage.
🧾 Smart Campuses and Cities: Optimization or Total Control?
Research on IoT in intelligent campuses confirms reduced energy consumption and improved logistics (S004). The system tracks student and faculty movements, analyzes classroom occupancy, optimizes schedules.
The publication doesn't disclose how long movement data is stored, whether it's used for performance evaluation, or shared with third parties.
- The Consent Problem
- Students and staff cannot opt out of the system without losing access to campus infrastructure. This isn't voluntary consent — it's coercion through architecture. The research doesn't discuss the ethical aspects of this model.
🔎 UAVs and IoT: Security or Mass Surveillance Tool?
IoT networks for unmanned aerial vehicle management enable coordination of multiple drones, territory monitoring, and real-time data transmission (S005). The technology is used for search and rescue, wildfire monitoring, infrastructure inspection.
The same systems are deployed for military reconnaissance, police patrols, and protest suppression.
| Application | Stated Purpose | Actual Risk |
|---|---|---|
| Search and rescue | Saving lives | Movement data without consent |
| Fire monitoring | Damage prevention | Surveillance of citizens in the area |
| Police patrols | Public safety | Mass surveillance of protesters |
The research focuses on technical aspects (communication protocols, energy efficiency), ignoring social consequences. There's no data on how often UAVs are used for surveillance without consent, legal restrictions, or their effectiveness.
🧬 AI and IoT Integration: Benefits and Drawbacks
Research on artificial intelligence integration in IoT acknowledges both advantages (automation, predictive analytics, personalization) and disadvantages (high energy consumption, debugging complexity, security risks) (S006). This is a rare example of balanced approach.
However, the publication doesn't quantify risks: how many AI-enabled IoT devices were hacked, how much data leaked, what's the average cost of an incident to the user.
Without concrete numbers, risk-benefit analysis is impossible. We know risks exist, but we don't know their scale. This makes informed user consent impossible.
🧪 Requirements Engineering: Why IoT Systems Are Designed Without Privacy
A systematic review of requirements engineering approaches shows that traditional methodologies focus on functional requirements, ignoring non-functional security and privacy requirements (S002). Modern approaches attempt to integrate "privacy by design," but the research provides no data on how widely these methods are applied in real projects.
- If privacy isn't built in at the design stage, it's impossible to add after the fact.
- Most existing IoT devices were designed in an era when privacy wasn't considered a priority.
- Firmware updates don't solve the problem if the architecture is fundamentally vulnerable.
This is a structural problem requiring a rethinking of development approaches, not cosmetic fixes.
Causality Mechanisms: Why the Correlation Between IoT and Data Breaches Isn't Coincidental — and Which Factors Amplify Risk
The connection between IoT proliferation and rising privacy incidents isn't simple correlation. Clear cause-and-effect mechanisms make IoT ecosystems structurally vulnerable. More details in the Logical Fallacies section.
🔁 Mechanism 1: IoT Economics Incentivize Excessive Data Collection
The business model of most IoT companies isn't based on selling devices (which are often sold at cost or at a loss), but on monetizing data. A smart speaker manufacturer doesn't profit from selling hardware, but from selling advertising based on analyzing your voice queries.
This creates a structural incentive to collect maximum data, even when unnecessary for the device's basic functionality. AI integration into IoT amplifies this trend: machine learning algorithms require large data volumes for training, justifying even more aggressive collection (S006).
The more data, the more accurate the model, the higher the profit. User privacy is an externality the market doesn't account for.
🧬 Mechanism 2: IoT Technical Complexity Creates User Opacity
The average user doesn't understand how IoT devices work. They don't know which sensors are active, what data is transmitted, where it's sent, or how long it's stored. Interfaces are deliberately simplified to avoid overwhelming users with technical details.
This creates information asymmetry: the manufacturer knows everything about you, you know nothing about what happens to your data. Even professional developers often don't understand the complete picture of data flows in complex IoT systems (S002).
- Information Asymmetry in IoT
- Manufacturers possess complete information about data collection, transmission, and storage; users don't. This creates conditions for hidden expansion of data collection without the device owner's knowledge.
⚙️ Mechanism 3: Absence of Security Standards in the IoT Industry
Unlike banking systems or medical equipment, the IoT industry has no mandatory security standards. A smart bulb manufacturer isn't required to undergo certification, hire security specialists, or conduct code audits.
This results in devices being released with critical vulnerabilities: default passwords, unencrypted data transmission, absence of firmware updates (S007).
| System Level | Security Requirements | Status in IoT |
|---|---|---|
| Banking Systems | Mandatory certification, audits, standards | Strict compliance |
| Medical Equipment | FDA approval, regular inspections | Strict compliance |
| IoT Devices | No mandatory standards | Voluntary compliance |
🧠 Mechanism 4: The Psychology of "Convenience" Suppresses Critical Thinking
IoT devices are designed to be maximally convenient: automatic setup, voice control, seamless integration. This creates a psychological trap: users become accustomed to convenience and begin perceiving it as the norm.
Any attempt to strengthen privacy (such as disabling data transmission) makes the device less convenient, which is perceived as punishment. This is a classic example of status quo bias: people prefer maintaining the current state, even when it's objectively worse than the alternative.
- Manufacturers maximize convenience at default privacy settings.
- Users become accustomed to convenience and perceive it as normal.
- Strengthening privacy requires disabling features, reducing convenience.
- Users choose convenience over privacy to avoid losing functionality.
IoT manufacturers exploit this by making privacy settings difficult to access and inconvenient. The connection between algorithms and dependency works here too: convenience becomes a trap that's difficult to escape without losing functionality.
Conflicts and Uncertainties: Where Sources Diverge — and What This Reveals About the State of IoT Research
Available sources demonstrate several zones of uncertainty where data is contradictory or absent. For more details, see the section Epistemology Basics.
🧩 Conflict 1: Effectiveness of Edge Computing for Privacy Protection
Some studies claim that on-device data processing (edge computing) solves the privacy problem, since data never leaves the device (S006). Others point out that metadata is still transmitted, and local processing merely creates an illusion of security.
There is no systematic comparison: how much information leaks through metadata versus payload. This isn't just a gap — it's a methodological blind spot.
🧩 Conflict 2: The Role of GDPR in Actual User Protection
Research (S001) shows that GDPR created a legal framework but didn't solve the technical problem: users don't know what data is collected and can't control it. Simultaneously, (S002) and (S007) document that architectural vulnerabilities in IoT systems exist independently of regulation.
The question remains open: can law compensate for technical design that doesn't incorporate privacy from the start?
🧩 Conflict 3: Healthcare IoT vs. Consumer IoT Specifics
Sources (S003) and (S005) focus on medical devices, where stakes are higher (patient life). But they don't provide a clear answer: do privacy threats differ qualitatively or only in scale?
| Parameter | Healthcare IoT | Consumer IoT | Status in Literature |
|---|---|---|---|
| Regulation | HIPAA, GDPR | GDPR, national laws | Documented |
| Architectural vulnerabilities | Described | Described | Parallel, not compared |
| Actual breaches | Isolated cases | Widespread, but not systematized | Data asymmetry |
🧩 Conflict 4: Who Bears Responsibility?
Sources (S004) offer recommendations but don't resolve the paradox: manufacturers can't guarantee network security, users can't control the device, service providers aren't responsible for architecture. Responsibility is diffused.
This isn't just an organizational problem — it's a systemic defect. When every participant can say "that's not my area," privacy becomes nobody's problem.
🧩 Conflict 5: User Behavior Data vs. Technical Reality
Research (S008) showed that smart speaker users worry about privacy but continue using the devices. Sources don't explain this gap: is it rational compromise, cognitive dissonance, or lack of information?
The question remains unanswered: can user awareness change behavior when technical alternatives don't exist?
📍 What This Reveals About the State of IoT Research
The literature documents problems but doesn't integrate them into a unified model. Each study operates in its own niche: (S001) — GDPR, (S002) — architecture, (S003), (S005) — healthcare, (S006) — user behavior.
- Cross-domain comparison is absent: how one vulnerability manifests across different contexts.
- No longitudinal studies: most work is a snapshot, not a trend.
- Recommendations are often technically unfeasible without redesigning the IoT ecosystem architecture.
- Gap between regulation and reality: laws rely on assumptions that research doesn't confirm.
The field exists in a state of fragmented knowledge. This doesn't mean the research is poor — it means the IoT privacy problem is more complex than any single discipline can encompass.
For developers, analysts, or users, this has practical implications: trusting individual recommendations is risky. You need your own threat model, built on understanding conflicts in the literature, not on its consensus.
