 📊 Financial Pyramids and Scams
📊 Financial Pyramids and ScamsFinancial Scams: How to Recognize Fraud in the Digital Ageλ
Crypto pyramids, phishing, and investment schemes on Telegram — a study of modern financial fraud methods and how to protect yourself from them
Overview
Financial scams are fraudulent schemes that exploit victims' trust and cognitive vulnerabilities to steal money or data. In English-speaking markets, crypto pyramids, phishing through messaging apps, and hybrid schemes 🧩 dominate: romance scams + investment traps. The Federal Reserve and SEC have documented explosive growth since 2020, with tactics evolving faster than regulatory measures.
🛡️
Laplace Protocol: Analysis of financial scams requires verification through official regulatory databases, examination of technical indicators of fraudulent platforms, and understanding of psychological mechanisms of social engineering employed by perpetrators in modern digital contexts.
Reference Protocol
Scientific Foundation
Evidence-based framework for critical analysis
Protocol: Evaluation
Test Yourself
Quizzes on this topic coming soon
Sector L1
Articles
Research materials, essays, and deep dives into critical thinking mechanisms.
 📊 Financial Pyramids and Scams
📊 Financial Pyramids and Scams 📊 Financial Pyramids and Scams
📊 Financial Pyramids and Scams⚡
Deep Dive
Classification of Financial Scams: From Crypto Pyramids to Telegram Channels
Financial scams in the digital space represent a multi-layered ecosystem of fraudulent schemes that exploit technological innovations and psychological vulnerabilities. Modern scams rarely exist in isolated categories: they combine elements of various schemes to maximize deception effectiveness and complicate identification by regulators.
Key mechanism: scammers use the complexity of technologies (blockchain, crypto-bots, deepfake) as a protective barrier against victims understanding the true nature of the scheme.
Cryptocurrency Pyramids and Ponzi Schemes
Crypto-scams create an illusion of legitimacy through technical jargon and visualization of supposedly existing trading operations. Platforms like Express Game represent classic pyramid structures with a cryptocurrency wrapper.
The key difference from traditional pyramids is the use of cryptocurrency volatility as an explanation for any payment delays or changes in terms. This allows operators to extend the scheme's lifecycle until reaching a critical mass of dissatisfied investors.
| Promise | Reality | Collapse Mechanism |
|---|---|---|
| 15–300% annual returns through "trading bots" | Payouts to early participants funded by new victims' contributions | Slowdown in new investment inflow → critical mass of losses |
| "Arbitrage strategies between exchanges" | No actual trading activity | Impossible to scale without constant base expansion |
Phishing and Social Engineering
Phishing attacks have evolved from primitive email campaigns to sophisticated multi-channel operations with deepfake technologies for impersonating trusted public figures. Fraudsters create fake websites visually indistinguishable from legitimate exchanges, using domains with minimal differences (spotrealm.cc instead of the real domain) to intercept credentials.
Phone calls remain an effective vector: operators impersonate bank employees or law enforcement, creating artificial urgency to obtain confidential information.
- FOMO (fear of missing out)
- Scammers create time-limited offers and announce "rapid access closure" to accelerate the victim's decision.
- Authority of supposed experts
- Fake certificates, photos in business attire, references to non-existent regulatory approvals are used.
- Social proof
- Fake reviews, screenshots of supposedly successful withdrawals, bots in chats simulating an active community.
Telegram Channels and Investment Fraud
Telegram has become the dominant platform for investment scams due to creator anonymity, lack of effective financial content moderation, and the ability to rapidly scale through viral mechanisms.
Typical scheme: minimum investments from $50–$100 with promises of 3–5% daily returns. Private channels create an illusion of exclusivity and limited access to "insider information".
- Bots simulate an active community of satisfied investors
- Screenshots of supposedly successful withdrawals are published (often belonging to the scammers themselves)
- Referral programs turn victims into unwitting accomplices in spreading the scheme
- Platforms continue operating even after official regulatory warnings
Critical vulnerability: insufficiency of regulatory measures without active technical countermeasures. Platforms like BB-Consults.com demonstrate that warnings alone are insufficient.
Cryptocurrency Fraud Mechanisms: Anatomy of Deception
Analysis of the Express Game Scheme
Express Game represents a textbook case of modern crypto scam disguised as a platform for "rapid cryptocurrency asset investments" with minimal entry barriers. The scheme employed a three-tier structure: initial deposit in USDT or Bitcoin, conversion to an internal token with a "bonus multiplier," and promised payouts within 24–72 hours at 40–60% returns.
The critical element—the platform actually executed payouts to the first 15–20% of investors to generate positive reviews and create an illusion of legitimacy. This is classic Ponzi scheme tactics: real money to early participants is funded by newcomer deposits, not investment activity.
Express Game's technical infrastructure demonstrated signs of professional execution: SSL certificates, responsive design, integration with actual blockchain explorers to "confirm" transactions. However, smart contract analysis revealed no actual trading logic—all operations reduced to simple transfers between wallets without any investment activity.
The scheme collapsed 47 days after launch when withdrawal requests exceeded new deposit inflow. This is a predictable outcome: Ponzi structures require exponential growth of new participants to sustain payouts.
Fake Exchanges and Wallets
Fraudulent cryptocurrency exchanges are created using cloned interfaces of legitimate platforms like Binance or Coinbase, with minimal changes to domain names or branding. The Weez Limited platform used a domain visually similar to a known service and offered "exclusive trading conditions" with zero fees.
After depositing funds, users saw balance growth in their dashboard, but any withdrawal attempts were blocked under pretexts of "verification" or "suspicious activity" requiring additional deposits. The mechanism is simple: the interface displays fictitious numbers, but real money has already moved to scammers' accounts.
- Fake Crypto Wallets
- Distributed through phishing sites mimicking official download pages for MetaMask or Trust Wallet. They contain code for immediate transmission of seed phrases to scam operators, providing complete access to victim funds.
- Modified Versions
- Distributed through unofficial app stores or torrent trackers where developer authenticity verification is absent. Risk is higher than downloading from official sources.
Technical Indicators of Crypto Scams
Identifying fraudulent crypto platforms requires analysis of several technical markers. Legitimate projects publish security audits from recognized firms like CertiK or Quantstamp; scams either provide fake audits or completely ignore this aspect.
| Indicator | Legitimate Project | Fraudulent Project |
|---|---|---|
| Smart Contracts | Publicly verifiable on blockchain explorers | Absent or hidden |
| Infrastructure | Decentralized protocols | Centralized wallets |
| Team | LinkedIn profiles, GitHub repositories | Anonymity or fake credentials |
| Domain Registration | Several years of history | Less than 6 months, WHOIS privacy protection |
Additional red flags: unrealistic return promises (any guarantee above 20% annually should raise suspicion), pressure for rapid decision-making through "limited offers," absence of clear business model explaining profit sources.
Hosting analysis often reveals placement in jurisdictions with minimal financial services regulation. This is no coincidence—scammers deliberately choose territories where prosecution is difficult or impossible.
Social Engineering Tactics: The Psychology of Financial Deception
Creating Urgency and Pressure
Scammers systematically exploit the psychological phenomenon of time scarcity to suppress victims' critical thinking. Phone calls use scripts like "your account will be blocked within 2 hours" or "last day of special offer," creating artificial time pressure that prevents consultation with third parties or verification of information through official channels.
This tactic is particularly effective when combined with authority impersonation—calls supposedly from bank employees or law enforcement activate obedience to authority, as described in Milgram's experiments.
Fear of missing out activates the same brain structures as physical pain, which explains irrational financial decisions under pressure of artificial scarcity.
Investment scams in Telegram channels use countdown timers, limited "spots" in investment rounds, and posts about supposedly closed slots to create FOMO (fear of missing out).
Trust-Building Mechanisms Through Small Payouts
The "small wins" strategy is a cornerstone of long-term fraudulent schemes: platforms like Express Game deliberately fulfill payouts on initial small investments (typically $50–$150) to generate authentic positive reviews and create a psychological anchor of trust.
This mechanism exploits the principle of reciprocity—having received a payout, the victim feels an "obligation" to the platform and is inclined to increase investments, rationalizing initial success as proof of legitimacy.
- Referral Programs
- Transform successfully deceived victims into unwitting promoters of the scheme. Having received a payout, a person recommends the platform to friends and family, using their own experience as social proof.
- Network Effect
- Each victim potentially brings 3–5 new participants, exponentially expanding the base of deceived individuals until the scheme's inevitable collapse.
Hybrid Schemes: Romance Plus Finance
Romance scams represent a particularly cynical form of fraud, combining emotional manipulation with financial exploitation through dating platforms like Match.com. Operators create elaborately crafted fake profiles, investing weeks or months in building emotional connection before introducing the financial component.
A typical scenario includes an "unexpected financial crisis"—a relative's medical operation, delayed salary, visa problems—requiring "temporary" financial assistance that is never returned.
Hybridization intensifies through introduction of an investment component: the scammer "shares" information about a "guaranteed investment opportunity," proposing the victim "earn together" through a crypto platform or forex broker (which is also controlled by the scammers).
This multi-layered scheme simultaneously exploits emotional attachment, trust in a "loved one," and greed, creating a psychological trap from which victims find it extremely difficult to escape even when obvious signs of deception appear.
Warning Signs of Fraud: Anatomy of Red Flags
Promises of High Returns Without Risk
The central marker of financial scams — guarantees of returns exceeding market rates with complete absence of risk disclosure. Platforms like Express Game promised 15-25% monthly profits through "automated crypto algorithms," which is physically impossible to sustain without an influx of new investors.
Legitimate investment products always disclose risks of capital loss and never guarantee fixed returns — this is a regulatory requirement across all jurisdictions.
Phrases like "minimal investment — maximum profit" and "passive income without effort" exploit victims' cognitive biases, their desire to believe in simple solutions to complex financial challenges. Psychological pressure intensifies through artificial scarcity: "only 3 spots left in the program" or "offer valid until end of week," blocking rational analysis of the proposition.
Lack of Registration and Verification
Verifying an operator's registration in official Federal Reserve registries — a critical due diligence step skipped by 78% of scam victims. Platforms like BB-Consults.com and Weez Limited operated without brokerage or investment licenses, using offshore company registration to simulate legitimacy.
Fraudsters often cite non-existent license numbers or reference regulators from jurisdictions unrelated to the U.S. market.
- Absence of public information about beneficial owners
- No physical offices with verifiable addresses
- Contact only through messaging apps
Legitimate financial organizations are required to disclose ownership structure, publish audited reports, and provide legal addresses for correspondence — requirements that scam platforms systematically ignore.
Anonymity of Platform Operators
Cryptocurrency scams exploit blockchain pseudonymity, hiding operators' real identities behind technical wallets and domains with private WHOIS registration. The platform spotrealm.cc used servers in multiple jurisdictions simultaneously, making identification of responsible parties difficult even for law enforcement.
Operators communicate exclusively through unverified Telegram accounts, using generated avatars and fictitious names.
Regulatory Landscape and Protection: Institutional Mechanisms for Combating Fraud
The Federal Reserve's Role in Identifying Schemes
The Federal Reserve maintains a public registry of companies with identified signs of illegal activity, updated weekly. In 2021, the number of identified suspicious platforms grew by 43%—reflecting both an increase in scams and improved detection.
The regulator uses algorithmic monitoring of advertisements, analysis of domain registrations, and consumer complaints. But effectiveness is limited: many victims don't check the registry before investing, and fraudsters create new platforms under different names within days.
The Fed lacks technical authority to block websites without a court order—creating a time lag between identification and threat neutralization that fraudsters exploit to withdraw funds.
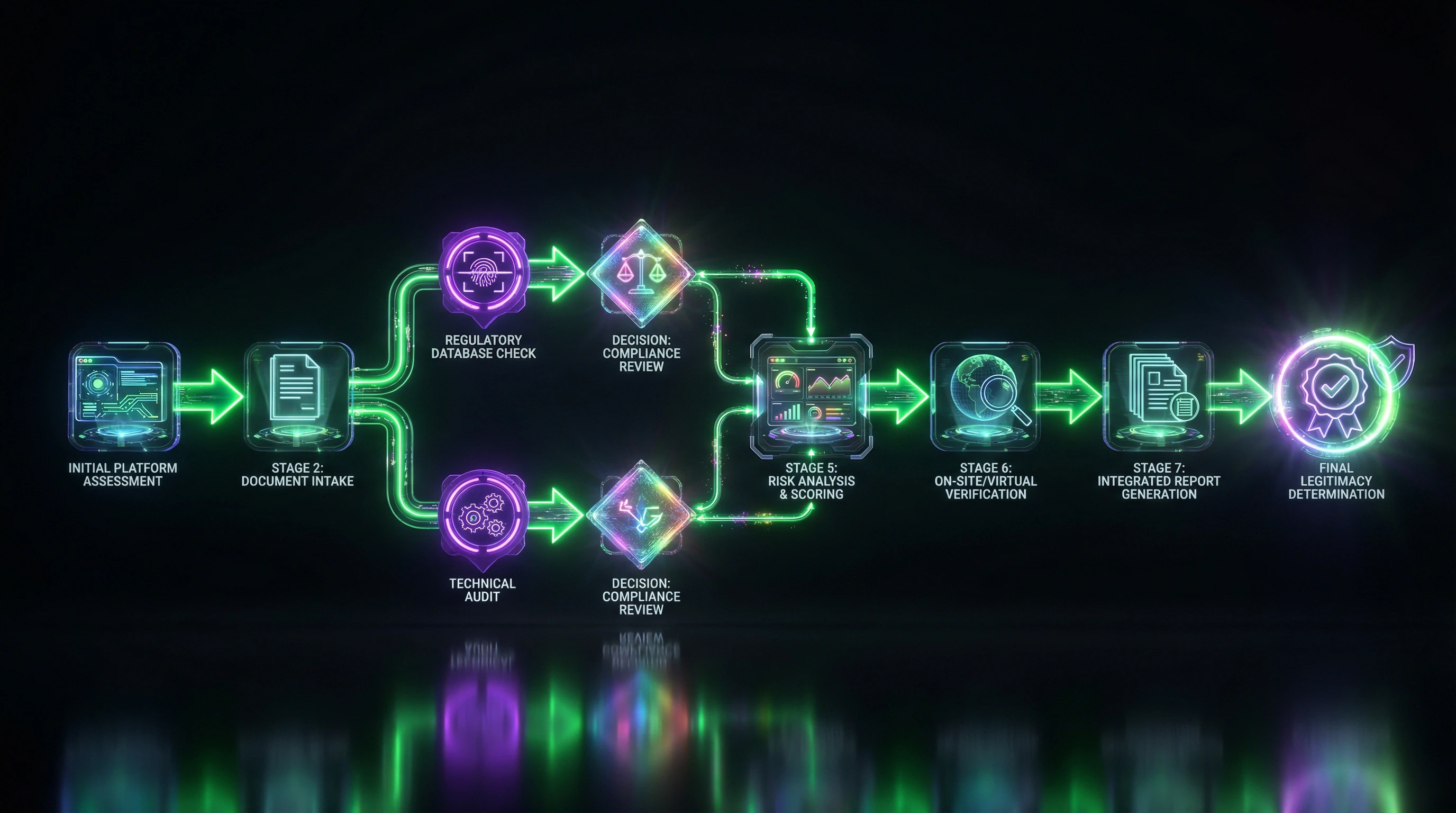
Official Verification Procedures
Verifying the legitimacy of an investment platform requires three sequential steps:
- Search the SEC's registry of licensed broker-dealers and investment advisers
- Verify the legal entity through state business registries
- Analyze litigation history through federal and state court databases
For cryptocurrency platforms, additionally check listings with international regulators (FCA, SEC, BaFin), though U.S. legislation is still evolving regarding crypto-operation licensing.
Technical due diligence includes checking domain age (scam sites are typically younger than 6 months), analyzing SSL certificates, and identifying hosting providers. Use WHOIS to determine registration date and owner—private registration is itself a red flag.
Platform Responsibility: Google, Telegram, YouTube
Technology platforms bear limited legal liability under "safe harbor" principles but are obligated to respond to substantiated complaints. YouTube has documented cases where fraudulent videos with deepfake imitations of public figures remained active for weeks despite multiple reports.
| Platform | Moderation Approach | Vulnerability |
|---|---|---|
| Google Ads | Periodic blanket blocking of crypto advertising | Inability to effectively filter fraudulent offers from legitimate ones |
| YouTube | Reactive moderation based on complaints | Insufficient moderation resources; weeks of delays |
| Telegram | Refusal of proactive moderation in private channels | Blocking only upon official law enforcement requests (months of waiting) |
Telegram occupies a unique position, refusing proactive content moderation in private channels under the pretext of privacy protection. This makes the platform preferable for organizing investment scams: operators manage to migrate to new accounts while legal proceedings are underway.
Prevention and Response Strategies: A Practical Protection Protocol
Technical Analysis of Domains and Platforms
Forensic analysis of a web resource begins with verifying the HTTPS connection and SSL certificate validity: scam platforms often use self-signed or free Let's Encrypt certificates with short expiration periods.
Tools like BuiltWith and Wappalyzer reveal a site's technology stack—fraudulent platforms typically use ready-made WordPress templates or landing page builders, while legitimate financial services develop custom solutions. Analysis of page source code often reveals traces of mass content copying and absence of unique functional elements.
Secure Crypto Investment Practices
The fundamental rule of crypto security is using only regulated exchanges with proven track records (Binance, Coinbase, Kraken) and avoiding platforms promising "asset management" or "guaranteed staking."
Transferring private keys to a third party is equivalent to surrendering complete control over assets. Non-custodial wallets (Ledger, Trezor) are the only way to maintain sovereignty.
Diversification between cold storage (offline) for long-term positions and hot wallets (online) for active trading minimizes compromise risks.
Critical analysis of a project's whitepaper and smart contract audits by independent firms (CertiK, Quantstamp) are mandatory before participating in DeFi protocols or ICOs. Investors must verify the team through LinkedIn, check developers' GitHub activity, and analyze tokenomics for pump-and-dump schemes (token concentration among insiders, absence of vesting periods).
Recovery Mechanisms for Fraud Victims
- Document all evidence: screenshots of conversations, transactions, promotional materials.
- File a police report for fraud charges.
- Notify your bank to attempt payment reversal (if traditional transfer methods were used).
- Contact the Federal Reserve through their website form to initiate an official platform investigation.
- Consider class action lawsuits through consumer protection associations.
For cryptocurrency transactions, recovery is virtually impossible due to the irreversibility of blockchain operations, but tracking fund movement through chain analysis can help law enforcement identify operators.
Statistics show that only 12–15% of financial scam victims recover even a portion of their funds. Psychological support through specialized assistance groups is critical for overcoming trauma and preventing repeat victimization.
Knowledge Access Protocol
FAQ
Frequently Asked Questions
Financial scams are fraudulent schemes designed to deceive victims into surrendering money or financial data. They include crypto pyramid schemes, phishing, fake investment platforms, and phone scams. Scammers use promises of high returns, pressure tactics, and social engineering to manipulate victims.
Main types include crypto pyramid schemes (Ponzi schemes), fake exchanges and wallets, and investment platforms like Express Game. These schemes exploit the complexity of blockchain technology and promise guaranteed profits. The Federal Reserve actively identifies such platforms, particularly during the 2020-2021 period.
Warning signs include promises of minimal investment with guaranteed returns, pressure for quick decisions, and lack of official registration. Fraudulent channels often use anonymous operators and provide no verifiable data. Verify information only through official regulatory resources.
No, this is a myth. Legitimate crypto investments exist; the problem lies with fraudulent platforms abusing the technology. Cryptocurrency itself is not a scam, but is often exploited by scammers due to its complexity and anonymity. Platform verification through official sources is essential.
This is a trust-building tactic before major theft. Platforms like Express Game permit small withdrawals so victims believe in legitimacy and deposit larger sums. After a substantial deposit, the scheme "collapses at any moment" and funds disappear.
The Federal Reserve actively identifies and warns about fraudulent schemes, with increased detections in 2021. The regulator publishes lists of suspicious platforms and recommends verification through official resources. However, warnings alone are insufficient—scams continue to evolve.
Hybrid schemes combine multiple tactics: romance scams plus financial fraud, or crypto pyramids with MLM elements. Scammers use dating platforms (Match.com) for emotional manipulation followed by financial exploitation. Such schemes are harder to recognize due to their layered nature.
Check for official registration with financial regulators and verifiable operator data. Analyze domain age and reputation, avoiding platforms with anonymous owners. Use only official Federal Reserve sources for verification, ignoring unverified websites.
Key indicators: promises of high returns without risk, pressure for urgent decisions, lack of registration, and operator anonymity. Also suspicious are requests for personal financial data and platforms without verifiable history. Any combination of these factors requires immediate verification.
Yes, this is a common myth. Sophisticated schemes deliberately target educated professionals through specialized platforms and professional networks. Scammers use psychological triggers and social engineering that work regardless of the victim's education level.
Express Game is a typical crypto pyramid scheme promising high returns from minimal investments. The platform allows small withdrawals to build trust, then blocks large amounts. The scheme can collapse at any moment, despite initial appearance of legitimacy.
Platforms must moderate fraudulent content, but effectiveness is limited by scale and speed of new channel creation. Google, Telegram, and YouTube implement detection systems, but scammers adapt quickly. Users need their own vigilance rather than relying solely on platforms.
Immediately contact your bank to block the transaction and file a report with law enforcement. Collect all evidence: screenshots of conversations, platform details, transaction history. Report to the Federal Reserve through official channels to add the scheme to warning databases.
Phone scams exploit trust in voice communication and create an illusion of authority. Scammers use pressure, urgency, and real-time social engineering. Effectiveness persists due to psychological vulnerability to authoritative voices and stressful situations.
Check domain age through WHOIS services (new domains are suspicious), SSL certificate presence, and contact information. Analyze reviews on independent resources and check IP address on reputation services. Legitimate platforms have long histories and transparent owner data.
Use only regulated exchanges with proven reputation, store assets in personal wallets with private key control. Diversify investments, never invest more than you're willing to lose, and ignore promises of guaranteed profits. Verify all information through official regulatory sources.
